Access,
Control, &
Delegation
Provide granular access roles to specific teams of Developers, Tiered Support Personnel, and/or individual users through groups.
ACCESS MANAGEMENT
Give the right people the right access to the right AWS accounts
Without long-lived credentials, shared keys, or spreadsheet provisioning. STS-brokered access with full audit trails and tenant isolation.
WHO THIS IS FOR
Built for teams who need secure, auditable access
From MSPs onboarding consultants to security teams enforcing boundaries without deploying IAM Identity Center per client.
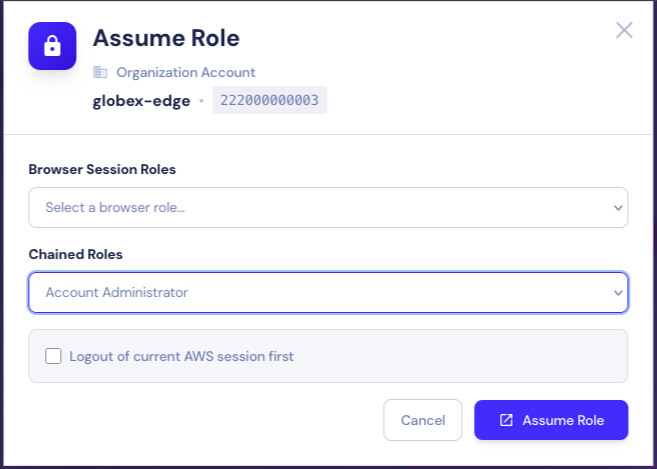
Three ways to assume a role. One UI.
🌐
Browser Session
Simplest option — opens AWS Console with the assumed role using your current session.
🔗
Federated Trust Role
Single-hop STS AssumeRole with system-generated External ID. Direct and secure.
⛓️
Chained Trust Role
Two-hop assumption through an intermediate "jump" account. Recommended for MSPs and high-security environments.
CORE FEATURES
Secure, granular, auditable
Users
Cognito-backed identity with MFA support (TOTP, Email OTP, SMS). Each user is bound to exactly one tenant via a tamper-proof, AWS-signed identity claim.
Multi-factor authentication options
Tenant-bound identity with tamper-proof claims
Profile management and account recovery
Direct user-to-resource access grants
Roles
Library Roles let you define a reusable role configuration once and reference it across many accounts. Server-authoritative External IDs prevent trust-policy spoofing.
Reusable role definitions across accounts
System-generated External IDs (no user customization)
Server-controlled session names for CloudTrail attribution
Group-based visibility controls
Teams
Invite team members via email with 30-day expiring invitations. Server-side seat-limit enforcement based on subscription tier.
Email-based invitations with expiration
Automatic seat-limit enforcement
Ownership transfer with full audit logging
Atomic team-membership transactions
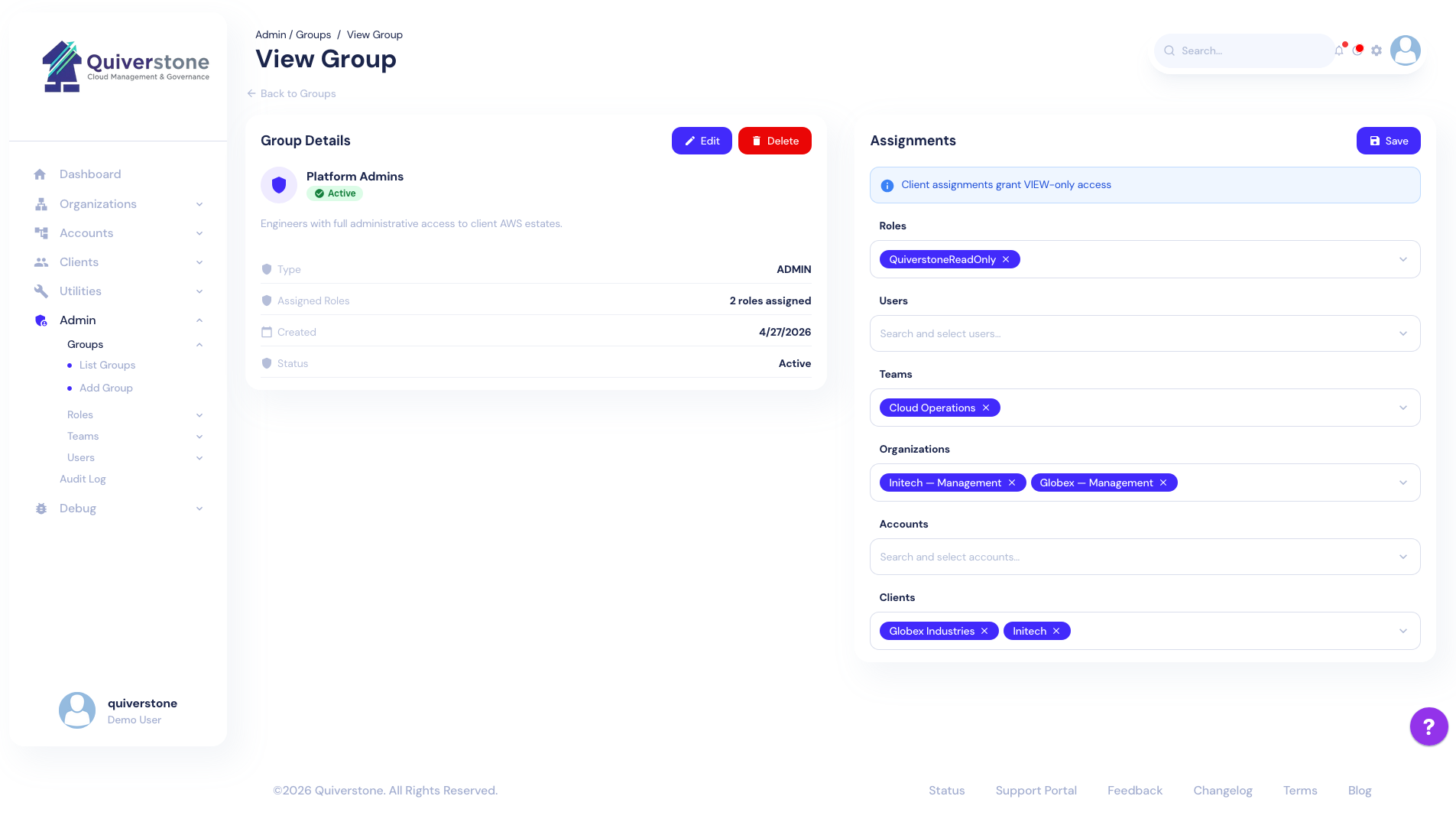
Groups
Bind resources (Organizations, Accounts, Clients, Roles) to grantees (Teams, individual users). Cross-tenant validation at write time ensures isolation.
Cross-tenant reference validation at write time
Real-time monitoring for unauthorized modifications
Immediate access revocation on Group deletion
Server-side enforcement — users can't bypass